05/19/2023
In our ever-evolving digital ecosystem, understanding the bedrock of digital assets—blockchain technology—is important to understand how they can impact our future and how we might use them.
To help us think about how these technologies might impact us in the future, we can compare blockchain protocols to the internet protocols we use every day. While almost everyone can send an email, few can explain how it works.
Two of those internet protocols we use every day are SMTP and HTTP.
Companies like Google and Microsoft employ SMTP for their email services, while web browsers make use of HTTP for us to browse the internet and view webpages. For all but a small percentage of users, we don’t understand the protocols or realize we’re using them.
The same might end up being true for blockchain technologies and digital assets.
Let’s demystify these complex systems and show how they operate on similar principles to help explain why we might not even know we’re using blockchain technologies in the future.
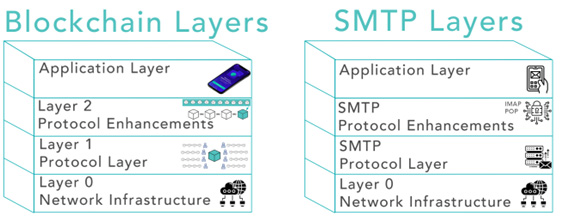
Unraveling the Blockchain Layers

You can think of blockchains as layers that stack on top of each other. Each layer adds more functionality to the system, building up from the very basic physical infrastructure to the applications that we see and interact with. Let’s start with the bottom layers.
1. Layer 0 – Network Infrastructure: This is the foundation of any digital system, blockchains included. It consists of the physical hardware (servers, routers, cables) and the internet protocols that handle data transmission, like TCP/IP.
2. Layer 1 – Protocol Layer: Here lives the heart of blockchain—the blockchain protocol. It sets the rules of the network, such as how transactions are validated and how consensus is reached. Examples are Bitcoin and Ethereum.
3. Layer 2 – Protocol Enhancements: These are enhancements to the base protocol designed to improve its functionality, speed and efficiency. This is where you’ll find solutions to the issues that plague many blockchains. These protocols or technologies are built on top of specific layer 1 blockchains.
4. Application Layer: This is the layer we interact with. It’s the user-facing applications—wallets, exchanges and decentralized applications (dApps)—that allow us to use blockchain technologies without needing to understand the intricate technical details.
Some applications are built directly on top of Layer 1 blockchains, but this might not be the best setup because of the disadvantages of Layer 1 blockchains, like transaction costs and scalability of transactions.
Layer 2 protocols are becoming a great layer to build applications on top of so they can take advantage of the efficiencies of these protocols.
SMTP: A Familiar Parallel
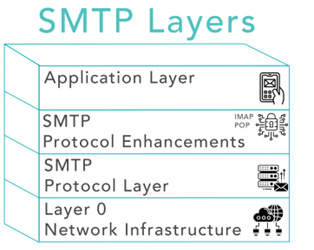
If you’ve ever sent an email, you’ve used Simple Mail Transfer Protocol (SMTP), the protocol for sending and receiving emails. It operates in a similar layered fashion to blockchains.
1. Network Infrastructure: SMTP, like blockchain, relies on internet infrastructure for communication and hardware for storage.
2. Protocol Layer: SMTP is the protocol that defines how mail servers communicate. It ensures the secure and reliable transmission of email across the internet.
3. Protocol Enhancements: Extensions to SMTP, like encryption layers and additional mail protocols such as IMAP and POP, enhance the functionality and efficiency of SMTP.
4. Application Layer: This is your email client—Gmail, Outlook, Apple Mail—providing a user-friendly interface for sending and receiving emails. This allows you to send and receive emails without understanding the underlying protocols or how they work or needing to set up your own email server.
One example of an application using blockchain protocols is WisdomTree Prime. Learn more at wisdomtreeprime.com.
The Invisible Technology of Digital Assets
Just as you don’t need to understand SMTP to send an email, the future use cases of blockchains will likely be invisible to most users. You won’t need to know how a smart contract works to use a decentralized application any more than you need to know how your car engine works to drive to work.
As more and more services migrate to blockchains, it will start to become more common that we are using blockchain technologies.
But why should we care about understanding the nuts and bolts of these technologies if they’re going to be invisible?
The answer lies in the crypto assets that are related to those blockchains.
We haven’t had assets tied to a potentially fundamental protocol like a blockchain before. With SMTP, there wasn’t a newly formed asset class tied to the protocol. You could invest in companies building the application layer or the technology, but that was it.
In addition to tokenized real-world assets on blockchains, some crypto assets are used to reward validators or miners who keep the network secure through their consensus mechanisms. If you want to learn more about the consensus mechanisms and how they work, this is a great explanation that dives deeper into them.
Looking Forward
Understanding these fundamentals gives us a better grasp of the digital landscape and where it’s heading.
As the saying goes, “The best way to predict the future is to create it.” By understanding the fundamentals of digital assets and blockchains, we position ourselves not as passive consumers of technology but as active participants in shaping our digital future.
So the next time you send an email, use your smartphone, surf the web or make online purchases, realize there is a vast amount of technology powering our actions, and blockchains might be added to the list.
Important Risks Related to this Article
This material is for informational purposes only and contains the opinions of the author, which are subject to change, and should not be considered or interpreted as a recommendation to participate in any particular trading strategy or deemed to be an offer or sale of any investment product, and it should not be relied on as such. This material is not intended to provide investment recommendations and is not an official statement of WisdomTree. This material represents an assessment of the environment discussed at a specific time and is not intended to be a forecast of future events or a guarantee of future results. Readers of this information should consult their own financial advisor, lawyer, accountant or other advisor before making any financial decision.
This material and all information contained in it or otherwise related to this material should not be relied on and is not a substitute for the skill, judgment and experience of the user, its management, employees, advisors and/or clients when making investment and other business decisions. All information is impersonal and not tailored to the needs of any person, entity or group of persons. None of the information constitutes an offer to sell or a solicitation of an offer to buy any security or other asset, financial product or other investment vehicle or any trading strategy.
Information provided by WisdomTree regarding digital assets, crypto assets, blockchain networks or technology providers should not be considered or relied upon as investment or other advice, as a recommendation from WisdomTree, including regarding the use or suitability of any particular digital asset, crypto asset, blockchain network or technology provider, or any particular strategy. WisdomTree is not acting and has not agreed to act in an investment advisory, sub-advisory, fiduciary or quasi-fiduciary capacity to any advisor, end client or investor and has no responsibility in connection therewith, with respect to any digital assets, crypto assets or blockchain networks, or otherwise.
There are risks associated with investing, including the possible loss of principal. Crypto assets, such as bitcoin and ether, are complex, generally exhibit extreme price volatility and unpredictability and should be viewed as highly speculative assets.
Crypto assets are frequently referred to as crypto “currencies,” but they typically operate without central authority or banks, are not backed by any government or issuing entity (i.e., no right of recourse), have no government or insurance protections, are not legal tender and have limited or no usability as compared to fiat currencies. Federal, state or foreign governments may restrict the use, transfer, exchange and value of crypto assets, and regulation in the U.S. and worldwide is still developing.
Crypto asset exchanges, liquidity providers, networks, protocols, settlement facilities, service providers and other participants in the digital asset ecosystem, and/or crypto assets related to the foregoing, may stop operating, permanently shut down or experience issues due to security breaches, fraud, insolvency, market manipulation, market surveillance, KYC/AML (know your customer/anti-money laundering) procedures, noncompliance with applicable rules and regulations, regulatory investigations or orders, technical glitches, hackers, malware or other reasons, which could negatively impact the price of any cryptocurrency traded on such exchanges or reliant on a digital asset ecosystem participant or otherwise may prevent access or use of the crypto asset.
Crypto assets can experience unique events, such as forks or airdrops, which can impact the value and functionality of the crypto asset. Crypto asset transactions are generally irreversible, which means that a crypto asset may be unrecoverable in instances where: (i) it is sent to an incorrect address, (ii) the incorrect amount is sent or (iii) transactions are made fraudulently from an account. A crypto asset may decline in popularity, acceptance or use, thereby impairing its price, and the price of a crypto asset may also be impacted by the transactions of a small number of holders of such crypto asset. Crypto assets may be difficult to value, and valuations, even for the same crypto asset, may differ significantly by pricing source or otherwise be suspect due to market fragmentation, illiquidity, volatility and the potential for manipulation.
Crypto assets generally rely on blockchain technology, and blockchain technology is a relatively new and untested technology that operates as a distributed ledger. Blockchain systems could be subject to internet connectivity disruptions, consensus failures or cybersecurity attacks, and the date or time that you initiate a transaction may be different than when it is recorded on the blockchain. Access to a given blockchain requires an individualized key, which, if compromised, could result in loss due to theft, destruction or inaccessibility. In addition, different crypto assets exhibit different characteristics, use cases and risk profiles.